Tens of thousands of computers around the world are getting locked up by a fast-spreading ransomware, shutting down huge international companies, government agencies and banks.
The cyber attack started with a business accounting program in Kiev, Ukraine. From there, it quickly spread to the nation's banks, electrical grid, airport and government offices before spreading to Russia, Europe and the world.
Australian companies, including Cadbury's chocolate factory in Tasmania, have also been impacted, and the Minister Assisting the Prime Minister for Cyber Security, Dan Tehan, warned on Thursday that the attack was far from over.
"With this type of ransomware attack, it can be days before we get further impacts," Tehan told Channel Seven's Sunrise program.
It's the second global ransomware attack in as many months, and it has got many in the security space worried, with experts warning the attacks are becoming increasing sophisticated -- and increasingly dangerous.
In May, Wannacry infected 300,000 computers globally and the flow-on effects are still being seen in Australia, including leading Victoria Police on Monday to suspend 590 speed and traffic offences, after the ransomware was found to have infected nearly 100 road safety cameras.
Here, we unpack why we're seeing a surge in global cyber attacks, and what you can do to protect yourself and your networks.
"Ransomware is basically a piece of malicious software, the short name for which is malware. It's just like a piece of software that you would buy and load onto your computer, but it is a bad piece of software," explained Steve Ingram, who is the Asia Pacific Cyber Leader at consultancy firm, PwC.
But not all malware is ransomware.
Malware is any software that infects your computer and acts without your control. It could include displaying a rude joke on your screen or manipulating or deleting important files.
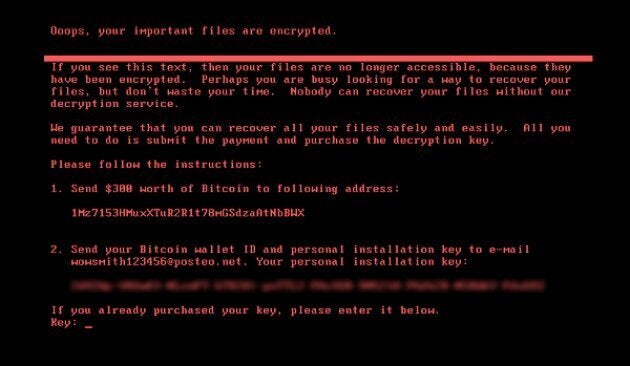
Ransomware is a more sophisticated type of this which, as its name suggests, generally involves a request for a "ransom". As was the case with both Wannacry and Petya, these attacks generally work by encrypting your files and locking you out of your computer.
"It demands you pay a penalty or fee or it threatens to do something with your data -- usually lock up your data or delete it -- although it could also threaten to publish it" said Dr Suelette Dreyfus, a cyber security lecturer at the University of Melbourne.
Ingram likened a ransomware attack to giving someone the keys to stay in your house and, when you return home from work, they have changed all the locks and you can't get it. The attack could pose as a legitimate email or present as a software update.
"It might look like a legitimate email from a friend or an organisation, but within the email there is an encryption key that locks out your hard drive," he said.
Ingram said that this week's 'Petya' attack is believed to have posed as a software update, although this is yet to be officially confirmed.
Petya has actually been around since last year, but the latest attack is believed to be a new, more aggressive "strain" of the virus.
Yes and no. Ransomware is not new -- in fact, Ingram says it's been around for most of the 21st century -- but the attacks are becoming more sophisticated, and reaching more and more people.
Cyber security experts attribute this in part to a new focus on this malware by criminals, but there is another, more worrying, reason behind the latest attacks.
In April, hackers were handed a new and explosive tool.
Hacking group Shadow Brokers gained access to a hacking tool, called Eternal Blue, believed to have been developed by the secretive US government's National Security Agency (NSA) and leaked it online. It's this tool that hackers used to rapidly spread both the Wannacry and Petya ransomware attacks.
And the hacking group have threatened to release more NSA hacking tools in the coming weeks.
Dr Dreyfus says the latest attacks raise important questions about the role of government agencies like the NSA in developing these security holes into hacking weapons, which governments use to tackle terrorism and other security threats, but are dangerous in the wrong hands.

"It raises important high-level questions around what societies should be authorising their governments to do in the cyber threat space. Is it ok for our government to stockpile these exploits? Is it ok for them to weaponise these security flaws? Or should they only be focusing on building defensive software to protect us?" Dr Dreyfus said.
"These are questions we used to think about in terms of nuclear armaments thirty years ago and now we're having to ask them about cyber weapons."
The attacks come days out from high-level government talks between Five Eyes nations (Australia, the United States, Canada, the UK and New Zealand) which will see Australia lead a push for "extreme surveillance" and more government control over data encryption.
"If you know that there is a security flaw in Windows and you write a program to use that flaw so that you can get control over Windows computers, it is incredibly powerful because it's not just able to break into one criminal's computer, it's actually potentially a weapon that can break into millions of computers," Dr Dreyfus explained.
And the more reliant on technology society becomes, the higher the stakes of any malware attack.
"Imagine if Wannacry or Petya were outbreaks in the future that caused driverless cars to go crazy on freeways en mass, to drive into houses, to drive into each other. It would be terrible, catastrophic," Dr Dreyfus said.
But the cyber security researcher said that while this was an important conversation that needed to be had, as a society we also need to keep things in perspective.
"You can get 90 percent of the protection you're going to need from doing a few simple things regularly," she explained.
The first and most important thing that you can do to protect yourself against ransomware is to make sure your computer is completely up-to-date. This includes not only your operating system (whether that's Microsoft Windows, Mac, Linux, Unix or another system), but also software like Microsoft Office, web browser Firefox, calendar applications and firewall software.
"Most systems will let you tick a box in your preferences to say please automatically update this software, and that makes it really easy to keep it updated. If you're running windows, you should update urgently," Dr Dreyfus said.
"(Software) companies spend a lot of money every year to run research labs to investigate malware affecting their products and to create vaccines for them, so take advantage of that."
Both Dr Dreyfus and Ingram also warn people against using illegal versions of software, which are less likely to have the latest updates.
The next thing to think about is investing in a sound anti-virus software -- or, if you already have one, ensuring it provides adequate protection and is up-to-date.
"It's not hugely expensive and it could save you a lot of heartache. It might be $50. You have to ask yourself: is it worth spending 50 bucks to prevent me losing all my data? For most people, the answer is yes," Dr Dreyfus said.
"There's a lot of anti-virus software out there, you can pick the one that is best for you. There are even some free programs that are helpful for protecting your data."
Another precaution to be wary of how you use your computer and what you click on, especially when it comes to emails and software updates.
"Make sure when you do get a (software) update, that it is legitimate," Ingram warned.
One way of doing this is to go directly to the software company's website and download the update from there. This is also another advantage of setting up automatic updates -- although Dr Dreyfus says you should still be checking the updates have been successful.
And when it comes to emails, if it looks suspicious, it probably is.
"The Federal Police don't do traffic offences outside of Canberra," Ingram said.

"If you get an email telling you to track your delivery and you haven't ordered a package, just be cautious around how you react to that email."
And if you receive an email from a friend that seems unusual, pick up the phone and check they actually sent it -- it's possible their device has been infected and the virus is spreading via their email contacts.
Finally, make sure you back up all your files regularly. The best system, Dr Dreyfus says, is to use an external hard drive or other storage device and back up according to a regular roster of, say, once a week.
While none of these measures guarantee 100 percent protection, they work similarly to a vaccine in that the more computers which are immunised against malware, the harder it is for these attacks to spread and reach global proportions.
That means that by making your own computer as secure as possible, you also help to protect others.
Once a ransomware infects one computer, it can spread to a whole network -- which is how the recent Petya attach reached Australia, via the Australian arms of international organisations.
"If more people had downloaded the upgrade from Microsoft in March this year, then fewer machines would have been infected by Wannacry," Dr Dreyfus said.
Prevention is always better than a cure, but if you've already been hacked by 'Petya' or any other ransomware, the first thing to know is not to pay the ransom money -- which in the case of 'Petya', takes the form of a request for $300 worth of Bitcoin.
"Unless there is an imminent threat to loss of life, you should never pay the ransom," PwC's Ingram said.
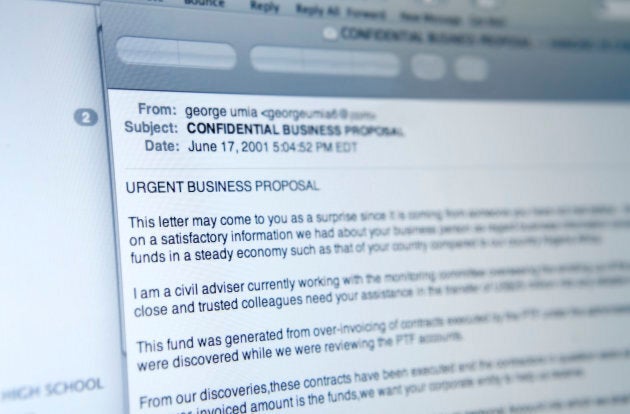
"It just encourages this sort of behaviour, and it's highly unlikely that they're going to return your access anyway. It is a bit like the old scam where you get an email saying 'give me your bank account details and we'll give you $5 billion' -- you never see the $5 billion."
The bad news is, if you've been attacked by the latest Petya ransomware and you don't have back ups, you're unlikely to be able to get your data back. This is because this attack is working at multiple levels. It not only encrypts your files, but also overwrites your master boot record (MBR) -- the part of your hard drive which locates your operating system and loads your computer.
Returning to the analogy of a house, Ingram said that ransomware usually just locks your front door, but the latest attack is also "changing the keys on your car, your garden shed, your garage. Once they get into your house, it's just self-generating."
ALSO ON HUFFPOST AUSTRALIA